
BEWARE OF MALICIOUS IMAGES —
Agency makes advise of Microsoft Retailer to restore faraway code-execution bugs in codecs library.
Dan Goodin
–

Microsoft has revealed unscheduled fixes for two vulnerabilities, one in every of them with a severity rating of great, that make it conceivable for attackers to influence malicious code on computer systems working any mannequin of Home home windows 10.
In distinction to the overwhelming majority of Home home windows patches, these launched on Tuesday had been delivered through the Microsoft Retailer. The frequent channel for working Scheme safety fixes is Home home windows Substitute. Advisories proper right here and proper right here talked about customers needn’t steal any movement to robotically obtain and set up the fixes.
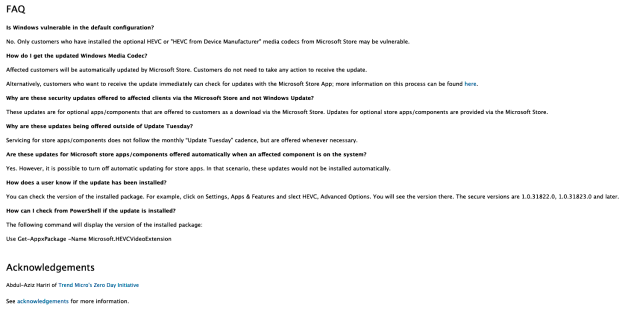
“Affected clients will probably be robotically up to date by Microsoft Retailer. Prospects originate no longer decide on to steal any movement to obtain the change,” each advisories talked about. “Alternatively, clients who decide on to obtain the change straight can verify for updates with the Microsoft Retailer App; extra recordsdata on this course of might perchance nicely nicely furthermore be came across proper right here.”
After I checked each the Microsoft Retailer and the Home home windows Substitute on my Home home windows 10 laptop computer, however, I noticed no affirmation that the patch had been connect in. On the final, Home home windows 10 customers can advise the Home home windows Substitute tab interior the Substitute and Security settings half to make sure patches had been connect in. The hyperlink provided inside the advisories provided no readability. Microsoft representatives didn’t straight reply to questions for clarification.
In a message obtained after this put up went are residing, the precise individual that came across the vulnerabilities, Abdul-Aziz Hariri of Pattern Micro’s Zero Day Initiative, confirmed theories a number of Ars readers believe made in feedback. They posited that that the change keen HEVC codecs, which can be historic in a Home home windows extension readily available from the Microsoft Retailer.
Important most essential readability
“The library affected is hevcdecoder_store.dll,” the researcher wrote. “That library is in charge for parsing HEIC pictures with HEVC codec. That library (extension) is readily available through the Home home windows Retailer. And since or no longer it’s a media codec downloaded from the Home home windows Retailer, I buy MS up to date it through the Home home windows Retailer and by no means the Home home windows Substitute.”
Additionally, since this put up went are residing, I managed to manually set up the change by opening Microsoft Retailer, clicking the three dots on the terminate correct, choosing Downloads and updates and pressing the blue Come by updates button inside the terminate correct. My Microsoft Retailer settings are configured to obtain app updates robotically, so or no longer it’s no longer apparent why Microsoft’s advisory says customers needn’t steal any movement to obtain the change.
In an electronic mail despatched after publication, a Microsoft guide talked in regards to the agency issued further steering. It says: “A safety change was once launched on June 30. Prospects who apply the change, or believe computerized updates enabled by strategy of the Microsoft Retailer, will probably be steady. We proceed to encourage clients to flip on computerized updates to help assure they’re steady.”
A FAQ inside the advisory has additionally been added to reveal that solely clients who believe connect in non-most essential HEVC or “HEVC from Scheme Producer” media codecs from the Microsoft Retailer believe inclined machines. Beneath are the FAQs as they firstly appeared and as they stand now.
Each vulnerabilities stay in Home home windows code libraries that take care of codecs historic to render pictures or different multimedia negate. Attackers can exploit the failings to influence code of their different or to construct up recordsdata saved on inclined packages. Exploits might perchance nicely nicely furthermore be delivered in notably designed picture recordsdata that imperfect pc reminiscence. Presumably, the pictures will probably be delivered on compromised web websites a goal visits or when targets beginning a malicious file despatched by electronic mail. Tuesday’s advisories didn’t recount if exploits labored solely when targets opened the malformed pictures specifically apps or any app.
Microsoft credited Abdul-Aziz Hariri of Pattern Micro’s Zero Day Initiative with discovering and privately reporting the bugs. Each advisories expose that there’s no longer any proof of the flaw being actively exploited inside the wild.
Put up up to date so as to add newly readily available particulars inside the fifth through ninth paragraphs. Headline modified to ponder the newly readily available recordsdata.
